March 26, 2026
Switching IT providers is a major decision, but a structured onboarding process can make the transition smoother and lower risk than many businesses expect. Most organizations complete core onboarding within 30 to 90 days, including system discovery, security improvements, support setup, and process stabilization. A well-managed transition helps reduce downtime, improve visibility, and create a stronger foundation for ongoing IT support.
Businesses across Central and Southeast Arkansas, including Little Rock, North Little Rock, Sherwood, and Pine Bluff, often switch IT providers when they need better communication, stronger cybersecurity, and more reliable support.
Understanding what happens during the first 90 days helps businesses feel more confident about making a change.
The 4 Phases of Switching IT Providers
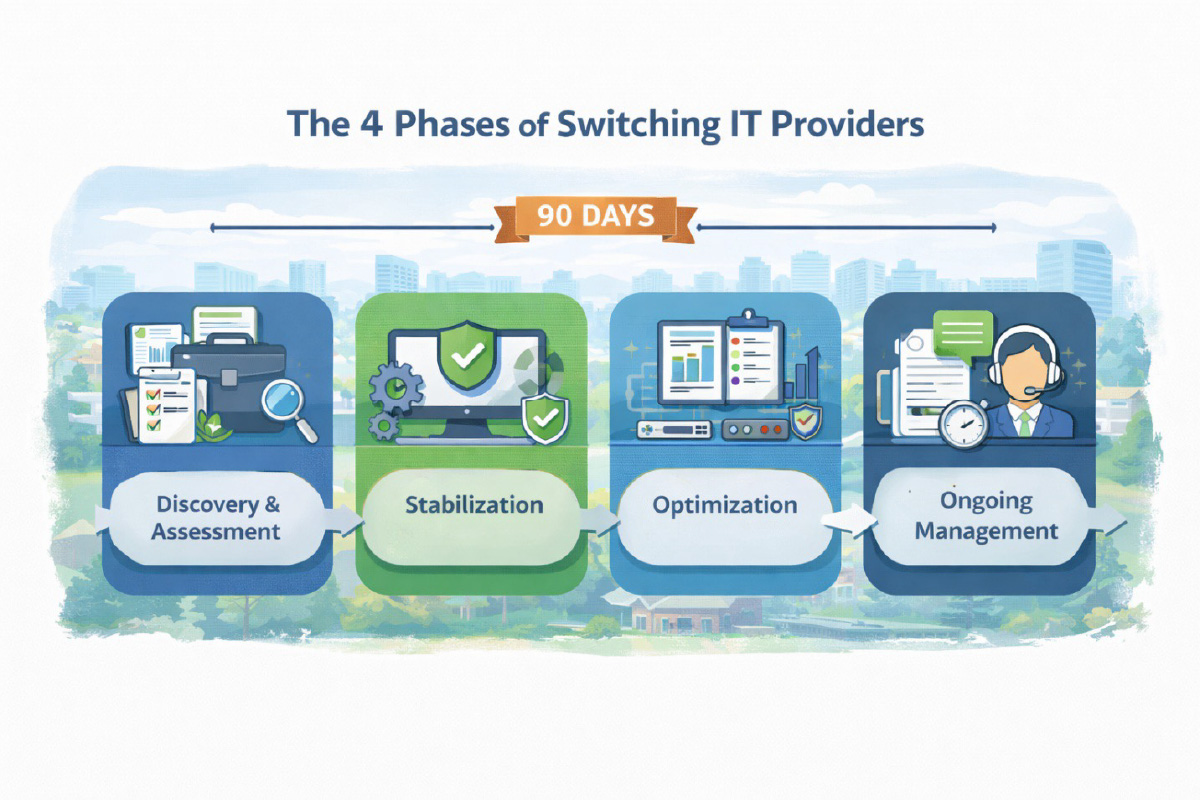
1. Discovery and Assessment
The first step is understanding the current environment.
This phase usually includes:
- device inventory
- network review
- user account review
- cybersecurity assessment
- backup evaluation
A clear assessment helps identify risks, gaps, and immediate priorities.
2. Stabilization
Once the environment is reviewed, the next step is stabilizing critical systems and support processes.
This often includes:
- resolving urgent technical issues
- securing weak points
- validating backup systems
- documenting key systems and vendors
Stabilization helps reduce operational risk early in the relationship.
3. Optimization
After urgent issues are handled, the provider can begin improving overall system performance and standardization.
This phase may include:
- patching inconsistencies
- security improvements
- network cleanup
- account access corrections
- documentation updates
Optimization helps businesses move from reactive IT to a more proactive model.
4. Ongoing Management
After the initial onboarding period, the business transitions into normal managed service operations.
This typically includes:
- proactive monitoring
- helpdesk support
- regular maintenance
- technology planning
- ongoing cybersecurity oversight
The goal is long-term reliability, better support, and fewer surprises.
Understanding Costs Before You Switch
Before making a change, many businesses want to understand the cost of managed IT services and how pricing is structured.
Our guide How Much Does Managed IT Cost in Little Rock? explains what businesses should expect when comparing providers and evaluating service plans.
Improving Security During the Transition
One of the most common reasons businesses switch providers is to improve cybersecurity and close security gaps that have been ignored.
Our guide What Cybersecurity Protections Should a 20–50 Employee Business Have in 2026? explains the key protections businesses should have in place.
Avoiding the Hidden Costs of Delayed Change
Staying with the wrong provider too long can create bigger problems, including downtime, security weaknesses, and unplanned spending.
Our guide 7 Hidden IT Costs Little Rock Businesses Often Overlook explains the real financial impact of reactive IT support and poor technology management.
Real Example: Government Agency
A government agency in Central Arkansas partnered with Mansour’s Computer Solutions after experiencing an email security breach. Without an internal IT department, they needed a reliable partner to secure their systems and provide dependable support.
The Mansour team responded the same day, resolved the issue quickly, and implemented stronger cybersecurity protections moving forward.
Their leadership shared the following feedback:
“Since partnering with Mansour’s Computer Solutions out of Little Rock, Arkansas, our company has seen a significant boost in both security and peace of mind. When we experienced an email breach, their team responded the same day, resolved the issue promptly, and gave us the confidence to entrust them with all our IT needs.
We had never worked with an IT firm before, and now we can't imagine needing anyone else. The team is responsive, professional, and genuinely committed to helping us succeed.
As a small business without an in-house IT department, Mansour’s has become an essential extension of our operations—keeping our systems secure and running smoothly. If you're on the fence, don’t be. Choosing Mansour’s was one of the best decisions we've made.”
— Government Agency Client, Central Arkansas
About Mansour Computers
Mansour Computers provides cybersecurity-focused managed IT services for small and midsize businesses throughout Arkansas, with a primary focus on Central and Southeast Arkansas.
The company regularly supports organizations across:
- Little Rock
- North Little Rock
- Sherwood
- Pine Bluff
- and surrounding Arkansas communities
With over 20 years of experience, Mansour Computers helps organizations with 10–50 employees maintain secure and reliable technology environments through proactive monitoring, cybersecurity protection, and predictable fixed-fee IT support.
Businesses without an internal IT department rely on Mansour Computers as a trusted technology partner to keep their systems secure and operating efficiently.
Book a Quick 10-Min Discovery Call Today!
If you're evaluating IT support for your business or want to improve your cybersecurity protection, schedule a quick discovery call with our team to discuss your needs and answer any questions.



