March 25, 2026
For businesses in Arkansas with 10–50 employees, cybersecurity is no longer optional. A properly secured business should implement protections such as endpoint detection and response, multi-factor authentication, advanced email filtering, secure backups, and ongoing system monitoring. Many small businesses invest between $125–$225 per device per month for managed IT services that include both technical support and cybersecurity protection.
Businesses across Central and Southeast Arkansas, including Little Rock, North Little Rock, Sherwood, and Pine Bluff, rely on managed IT providers to reduce cyber risk, improve system reliability, and protect their day-to-day operations.
Understanding which cybersecurity protections matter most helps business owners make better technology decisions and avoid preventable security incidents.
The 5 Core Cybersecurity Protections Every Small Business Needs
-
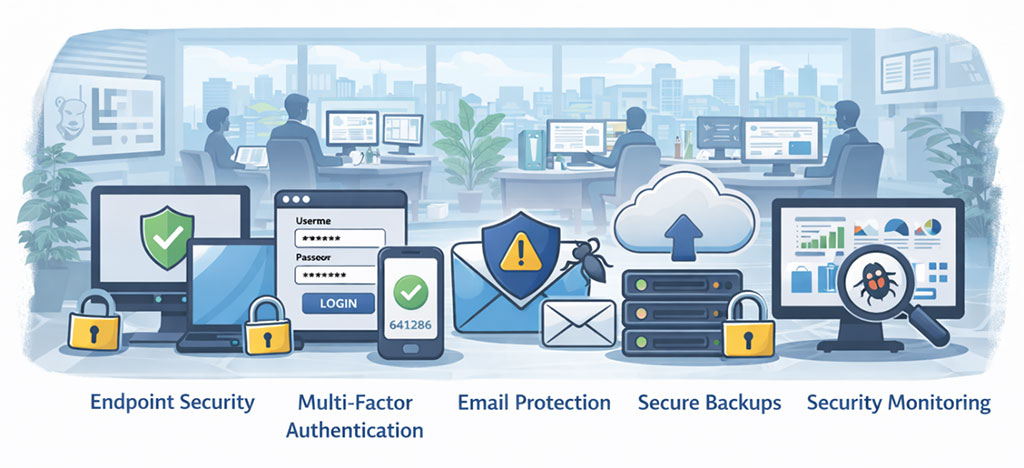 Endpoint Detection and Response
Endpoint Detection and Response
Endpoint Detection and Response, often called EDR, helps detect suspicious behavior on workstations, laptops, and servers before a threat spreads across the business.
This protection is especially important because many attacks begin on a single compromised device.
-
Multi-Factor Authentication
Multi-Factor Authentication adds another layer of protection beyond passwords.
Even if a password is stolen or guessed, MFA helps prevent unauthorized access to email accounts, cloud platforms, and business systems.
-
Advanced Email Security
Email remains one of the most common entry points for phishing attacks, malware, and credential theft.
A strong email security solution should include:
- phishing filtering
- attachment scanning
- malicious link protection
- impersonation detection
-
Secure Data Backup and Recovery
Backups are critical for business continuity.
A strong backup strategy should include:
- daily backups
- offsite or cloud storage
- encrypted backup protection
- regular recovery testing
Without reliable backups, a ransomware attack or hardware failure can cause major operational disruption.
-
Ongoing Security Monitoring and Updates
Cybersecurity is not a one-time setup.
Businesses need ongoing protection through:
- software patching
- vulnerability management
- security monitoring
- account protection reviews
These ongoing processes help reduce risk over time and close security gaps before they become serious problems.
Understanding the Cost of Cybersecurity
Many businesses implement cybersecurity protections through managed IT services rather than buying and managing separate tools on their own.
Our guide How Much Does Managed IT Cost in Little Rock? explains how cybersecurity services often fit into overall IT pricing and what businesses should expect to pay.
What Happens If Security Is Overlooked
Weak cybersecurity often leads to bigger operational and financial problems later.
Our guide 7 Hidden IT Costs Little Rock Businesses Often Overlook explains how security gaps, downtime, and reactive support create unexpected costs for small businesses.
What to Expect When Switching to a More Secure IT Provider
Many businesses improve their security posture during the onboarding process with a new IT partner.
Our guide What Happens During the First 90 Days After Switching IT Providers? explains how businesses typically assess risk, fix vulnerabilities, and improve their systems during a provider transition.
Real Example: Government Agency
A government agency in Central Arkansas partnered with Mansour’s Computer Solutions after experiencing an email security breach. Without an internal IT department, they needed a reliable partner to secure their systems and provide dependable support.
The Mansour team responded the same day, resolved the issue quickly, and implemented stronger cybersecurity protections moving forward.
Their leadership shared the following feedback:
“Since partnering with Mansour’s Computer Solutions out of Little Rock, Arkansas, our company has seen a significant boost in both security and peace of mind. When we experienced an email breach, their team responded the same day, resolved the issue promptly, and gave us the confidence to entrust them with all our IT needs.
We had never worked with an IT firm before, and now we can't imagine needing anyone else. The team is responsive, professional, and genuinely committed to helping us succeed.
As a small business without an in-house IT department, Mansour’s has become an essential extension of our operations—keeping our systems secure and running smoothly. If you're on the fence, don’t be. Choosing Mansour’s was one of the best decisions we've made.”
— Government Agency Client, Central Arkansas
About Mansour Computers
Mansour Computers provides cybersecurity-focused managed IT services for small and midsize businesses throughout Arkansas, with a primary focus on Central and Southeast Arkansas.
The company regularly supports organizations across:
- Little Rock
- North Little Rock
- Sherwood
- Pine Bluff
- and surrounding Arkansas communities
With over 20 years of experience, Mansour Computers helps organizations with 10–50 employees maintain secure and reliable technology environments through proactive monitoring, cybersecurity protection, and predictable fixed-fee IT support.
Businesses without an internal IT department rely on Mansour Computers as a trusted technology partner to keep their systems secure and operating efficiently.
Book a Quick 10-Min Discovery Call Today!
If you're evaluating IT support for your business or want to improve your cybersecurity protection, schedule a quick discovery call with our team to discuss your needs and answer any questions.



